As part of my Running my business from an iPhone 6 Plus project, I need to access computers on my LAN at work from my iPhone 6 Plus while traveling. After trying several approaches, the best solution seems to be through setting a VPN (virtual private network), which allows my phone to make an encrypted connection to my LAN at work. This provides secure access to all of the resources I have there, which I’ll cover on a separate blog entry.
My firewall/router is a Netgear SRX5308, and over the years, I’ve tried setting up a vpn to my iPhone, but never succeeded. This time around I did get it going with IOS 8.1.
Here’s what I did:
Setting up the firewall/router:
My router has the latest firmware available from Netgear:
| System Name: | SRX5308 |
| Firmware Version: | 4.3.1-22 |
The process of setting up the router includes these three steps:
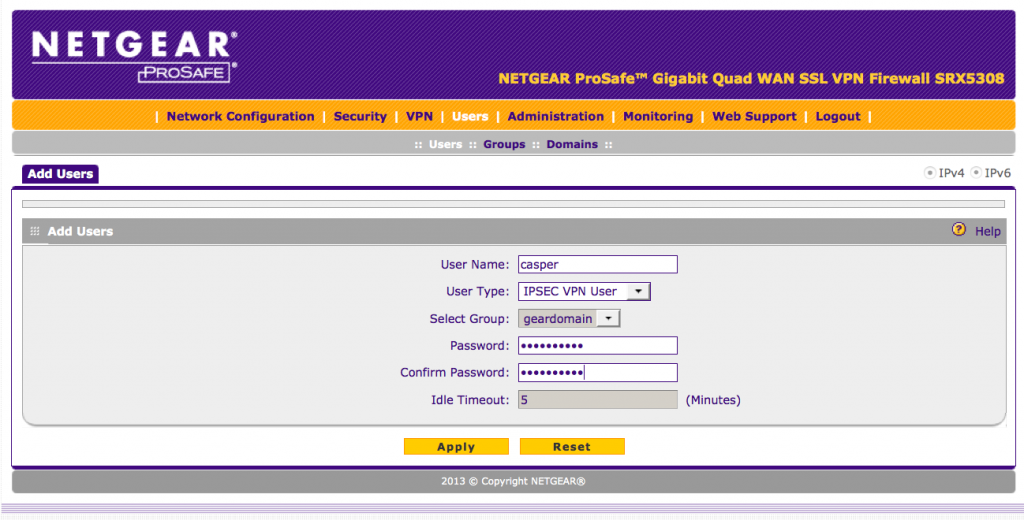
Add a user/password, for the login and password you’ll need when setting up the connection on the phone. Log into the router, and under the user menu, ‘add user’:
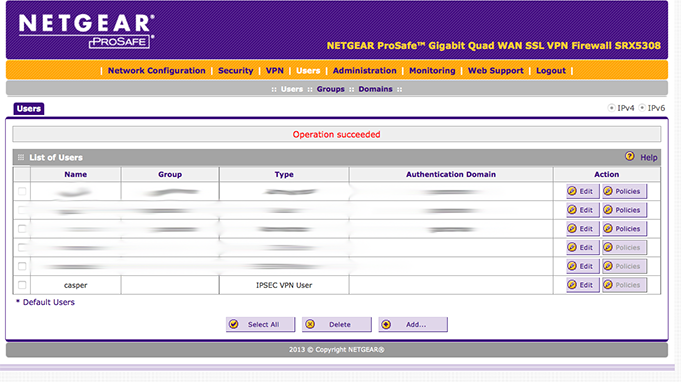
Then hit ‘APPLY’, and you’ll get confirmation that the user has been added:
Add a mode config record
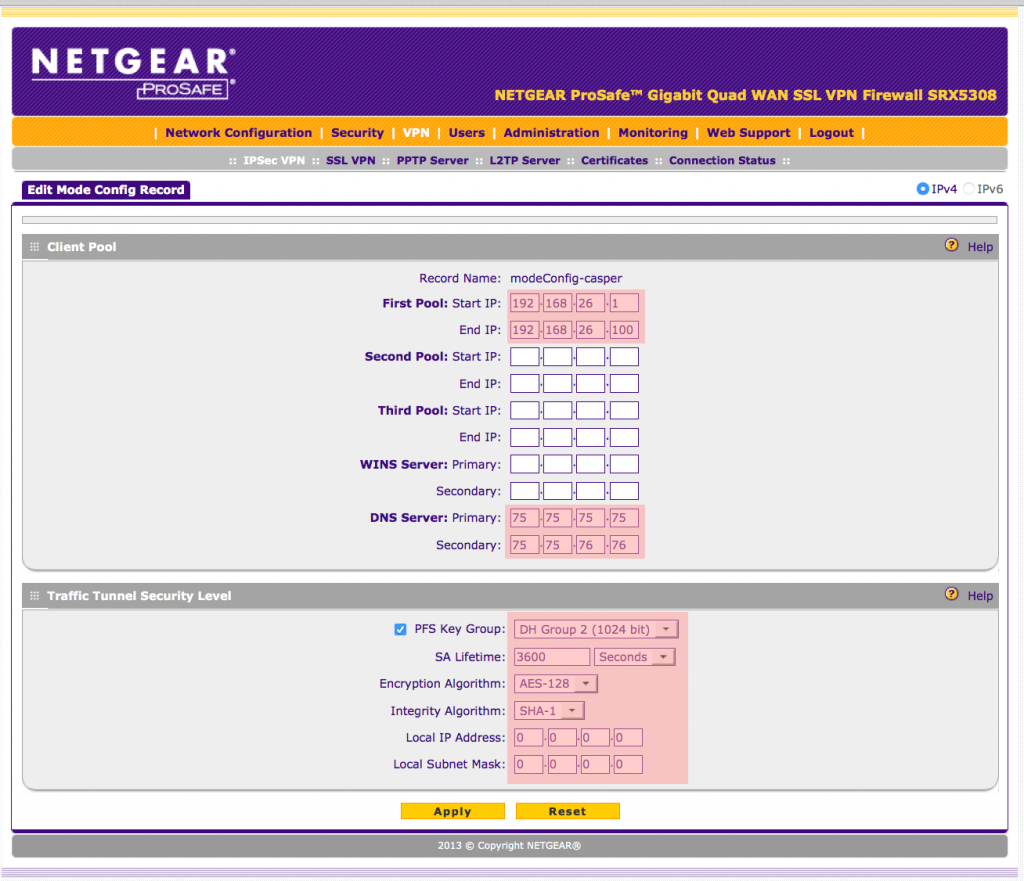
Under “VPN”, “IPsec”, select the “Mode Config” tab, and then “Add…’ and fill in the screen:
The first pink area specifies a pool of ip’s that will be used for the connecting devices. Make sure these ARE NOT on you lan that want to connect to…
The second pink area specifies the DNS servers that computers on your LAN see… Filling these in allows your remote device to lookup and browse computers that are not on the LAN.
The third pink area specifies the settings you should select… note that the “Local IP Address” and “Local Subnet Mask” are both set to 0.0.0.0
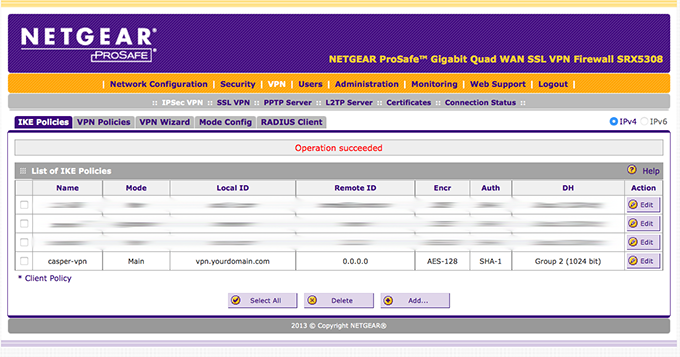
Setup an IKE policy for the connection
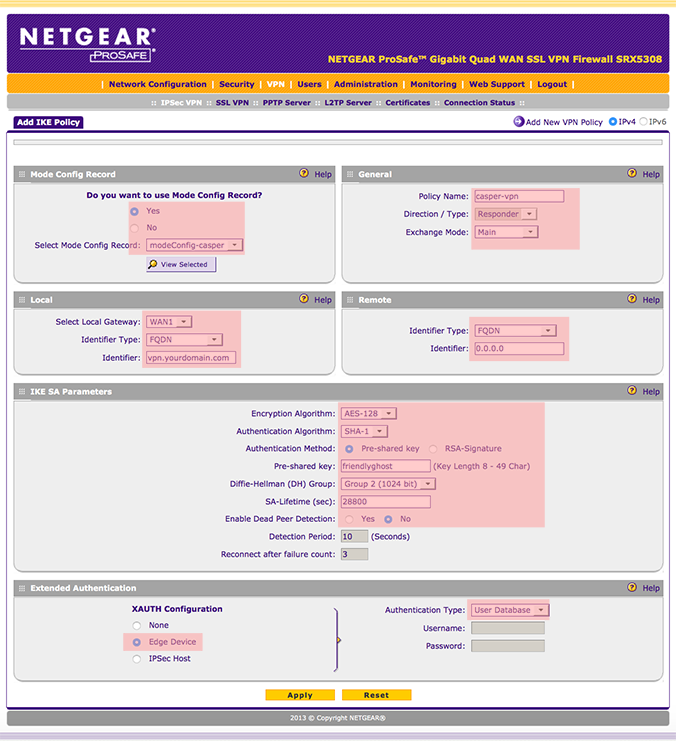
Under “VPN”, “IKE policies”, select “Add…” to get to the following screen:
Select “Yes” and the name of the mode Config, i.e. modeConfig-casper.
Give this IKE Policy a name, and select MAIN (Agressive WILL NOT WORK with IOS)
Under Local, specify the FQDN of the WAN, or IPADDRESS and the IPaddress of the wan. You would put your FQDN of the wan address where ‘vpn.yourdomain.com’ is on the above image.
For Remote, select FQDN, and type in 0.0.0.0 This allow you to log in from any ip address.
For IKE SA Parameters, select AES-128, SHA-1, pre-shared key, type in a keyphrase (our example uses ‘friendlyghost’), DH = Group 2, SA-Lifetime = 28800, Enable Dead Peer Detection = no.
Finally, for Extended Auth, select ‘Edge Device” and ‘User Database’
Press apply, and get to this screen that confirms the new policy:
That’s it for the SRX5308 setup.
Now, onto the setup for the iPhone…
First of all, make sure your iPhone is up to date… “Settings”, “General”, “Software Update”…
Staying up to date is generally a good practice… in this case, it’s mandatory.
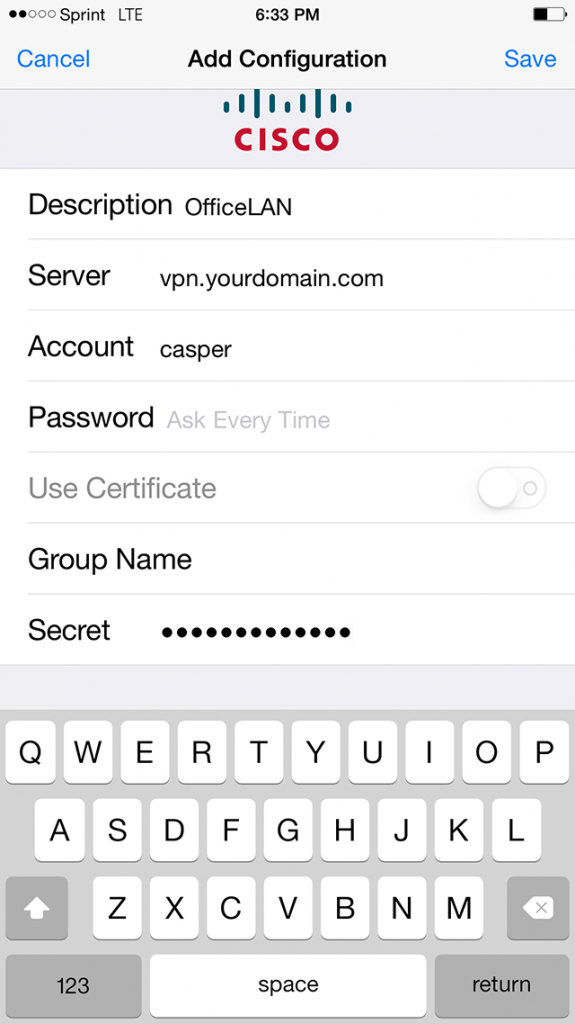
Add a VPN Configuration…
“Settings”, “General”, “VPN”, “Add a VPN Configuration…”, choose “IPSec” to get to this screen:
Give the connection a name – OfficeLAN
Then, fill in the values for the VPN that we just setup on the router….
Server: FQDN or IP Address of the router wan port
Account: casper
Secret: friendlyghost
Then “Save”
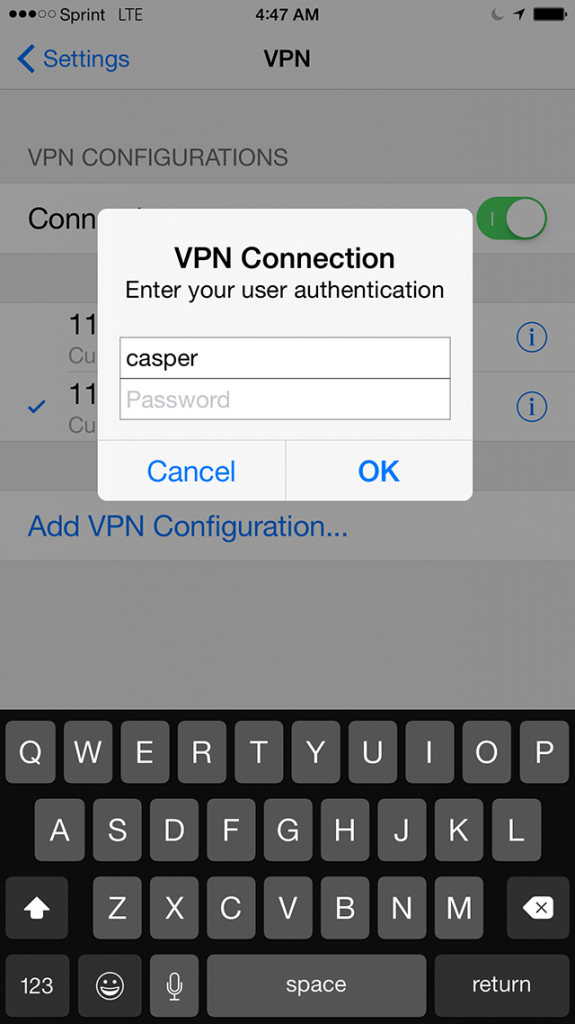
Test it out….
Once you are logged in to the vpn:
You get a VPN annunciator at the top of the screen, indicating that the VPN connection is active.


It has been an extremely frustrating effort trying to get my ipad working with vpn to my SRX5308. Finally works! Thanks for your excellent tutorial on this, go it working now in 5 minutes!
Hi Ken, I feel your pain… ! I was so happy when I got it going, I figured it would help others if I posted the solution. Glad it helped! Dan
This is perfect, thanks. However, once the VPN is active I still cannot browse to anything, external or internal. Ideally I need to browse using the iPad safari browser to my intranet site or external sites such as net gear.co.uk, plus others. It there something else I need to do, with firewall or ports or routing maybe to complete the process?
Hi Dave, The article and settings are what I use, and I can browse both on the LAN and on the internet. It works with both an ipad and an iphone.
I’d suggest that you check all of your settings, when you activate the vpn, you should get a page where you type your vpn password. Just to be sure, make sure your network address of your ipad has a different ip address than the one you are logging into. I.E., if your lan is something like: 192.168.4.x, make sure that you are on a different subnet address before you initiate the vpn connection. (you don’t want your ip address to be 192.168.4.197, and then login to your vpn, to a lan address where the subnet address is 192.168.4.x)